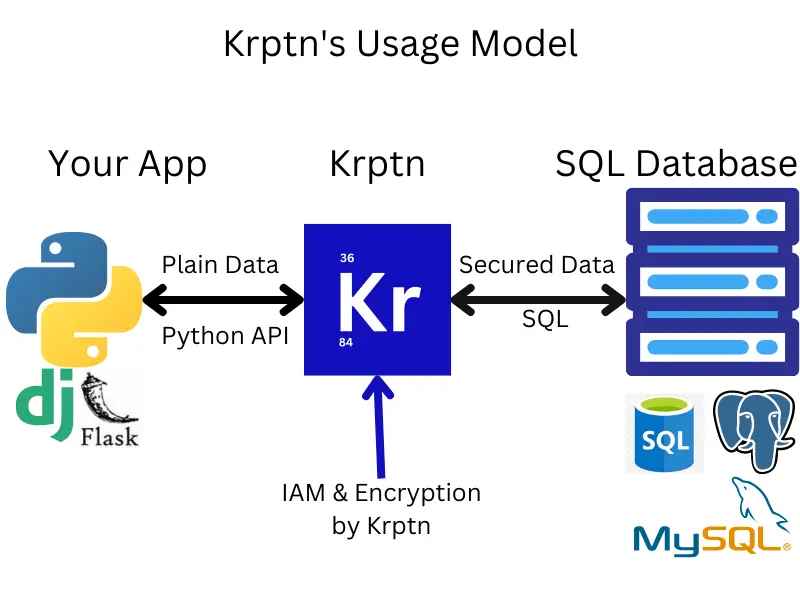
We all love Django and other web frameworks! However, their primary focus is creating websites - not securing them. One example is Django's built-in authentication system. While it hashes the password, it does not encrypt user data for you. Encryption is left to the developer...
Wouldn't it be nice if encryption would also be handled by the IAM? Perhaps it could be handled in a zero knowledge model, such that, without the user entering credentials, not even the database administrator can read it?! This is exactly what we do! Please see our documentation, homepage or continue here, on our GitHub, for more information!
To prove that such is possible, we have a Flask and Django example on GitHub.
Quick Install:
pip install krptnWe are building a user authentication and access management system (IAM) with Zero Knowledge security. It is available as a python extension module. However we have certain limitations.
How we achieve this?
- All data is encrypted (any data can be requested by the developer to be secured)
- Only the appropriate users' credentials can unlock the cryptosystem (this protects you from server-side attacks)
This gives you Zero Knowledge security (one of the most secure available) without ever needing to even notice it! It protects you from server side attacks.
- Secure Storage of Data
- User Authentication
- FIPS Validated Cryptography (via OpenSSL 3)*
- Secure memory wiping (except on PyPy)
- FIDO Passwordless*
- Integration with popular web frameworks
* FIDO (passwordless) does not use FIPS validated resolvers
from krypton import basic
# Create an instance of Crypto - a class for encrypting and storing sensitive data.
myCrypto = basic.Crypto()
pwd = "Perhaps provided by the user"
# It supports C.R.U.D. operations:
dataId = myCrypto.secureCreate("Example data", pwd) #id is an integer
print("The data is:")
print(myCrypto.secureRead(dataId, pwd)) # prints Example dataSee User Auth.
To use FIDO with User Auth, please see Krptn's FIDO Documentation.
This module uses a custom Key Management System for AES-256 Keys. See KMS for more information.
Note: we have considered using HSM as key management systems. We, however, have decided that we will not integrate HSMs because it would be difficult to maintain Zero Knowledge security.
Of course, all data is securely encrypted even if it is not via a HSM!
If you want, you can encrypt the SQL database using HSM managed keys for additional security.
Here is an example for how to set the database to be used:
import krypton
krypton.configs.SQLDefaultCryptoDBpath = "sqlite+pysqlite:///Path/example.db"
krypton.configs.SQLDefaultKeyDBpath = "sqlite+pysqlite:///Path/key.db"To see what these settings strings should contain please see Databases.
We would love to learn how you use our project! Our email is [email protected], and we would appreciate if you could drop us a note about your interactions with Krptn.