Checkov is a static code analysis tool for infrastructure-as-code. It scans cloud infrastructure provisioned using Terraform and detects security and compliance misconfigurations.
Checkov is written in Python and provides a simple method to write and manage policies. It follows the CIS Foundations benchmarks where applicable.
- 50+ built-in policies cover security and compliance best practices for AWS, Azure & Google Cloud.
- Policies support variable scanning by building a dynamic code dependency graph (coming soon).
- Supports in-line suppression of accepted risks or false-positives to reduce recurring scan failures.
- Output currently available as CLI, JSON or JUnit XML.
Scan results in CLI
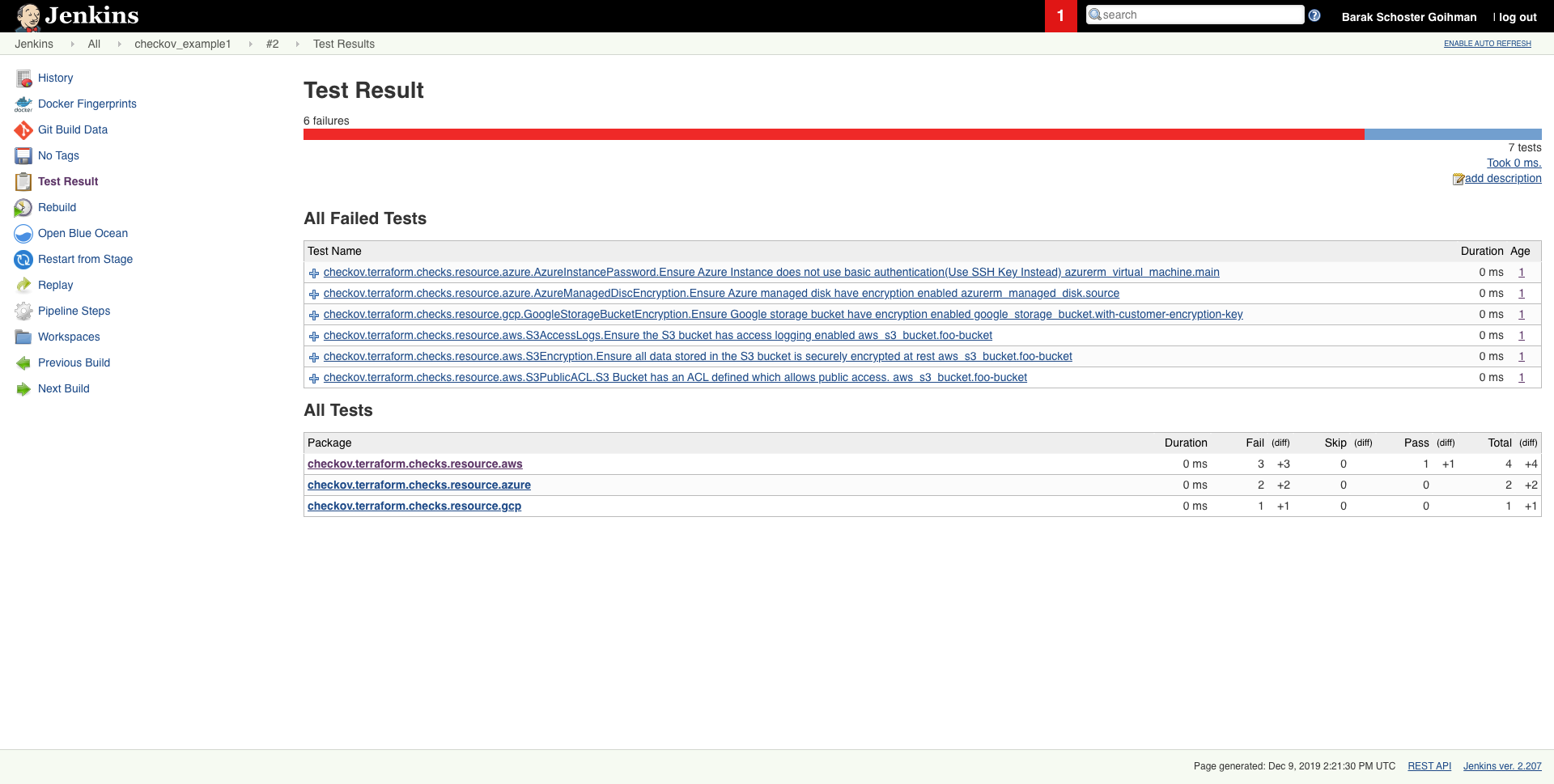
Scheduled scan result in Jenkins
pip install checkovcheckov -d /user/tfOr a specific file
checkov -f /user/tf/example.tfPassed Checks: 1, Failed Checks: 1, Suppressed Checks: 0
Check: "Ensure all data stored in the S3 bucket is securely encrypted at rest"
/main.tf:
Passed for resource: aws_s3_bucket.template_bucket
Check: "Ensure all data stored in the S3 bucket is securely encrypted at rest"
/../regionStack/main.tf:
Failed for resource: aws_s3_bucket.sls_deployment_bucket_name Start using Checkov by reading the Getting Started page.
docker pull bridgecrew/checkov
docker run bridgecrew/checkov -i -v /user/tf:/tf -d /tfFor Terraform compliance scanners check out tfsec, Terrascan and Terraform AWS Secure Baseline.
For CloudFormation scanning check out cfripper and cfn_nag.
Contribution is welcomed!
Start by reviewing the contribution guidelines. After that, take a look at a good first issue.
Looking to contribute new checks? Learn how to write a new check (AKA policy) here
Bridgecrew builds and maintains Checkov to make policy-as-code simple and accessible.
Start with our Documentation for quick tutorials and examples.
If you need direct support you can contact us at [email protected] or open a ticket.