Comments (12)
I think the main problem with any kind of classification is that it really depends on the organization, what their doing, what level of risk they are willing to tolerate. That is sort of why we went with 'level' of risk rather than any kind of specific point or grade level, at least right now.
We figured it'd properly note that something might be at high risk of causing a problem if there was a misconfiguration, but you could mitigate many of the challenges if proper attention was paid.
Things like any resources that are public are high risk because its very easy to not properly apply security groups/other controls. Un-rotated access keys were high risk for us because it implied that the user hadn't been used in a while or might have broad permissions. Public S3 buckets are high risk because there is almost no reason to do that in most configurations.
Many of the CloudWatch Logging group items are lower risk for example because they don't lead to exposure of anything. SGs not in use is lower risk because they aren't actually being used
from prowler.
Would be good if there's a way to model it the same way the CIS-CAT tools scores for other benchmarks.
from prowler.
Yes, I have to look at it but my initial thought was to add a % per check because it will depends on the items to review on each check, then each check will give a value from 0 to 100 then the total scoring index would be the average of all checks.
from prowler.
Looking at their documentation and a sample report I have just created in my laptop it looks like it works in the same way or pretty similar to how I said.
from prowler.
👍
from prowler.
We've also talked about doing some kind of easy to digest score for accounts, though we ended up classifying each check based on high, medium, low risk.
from prowler.
Cool @sidewinder12s! Can you share that classification? I have tried to think the best way to score the checks but I don't know how to implemented and also make it work with any extra/future check, since more checks are coming as usual.
For instance, if you have properly set the password length you get 1 point but if you have 3 out of 10 security groups with SSH open to the internet, is that a -3? I don't know... With the current amount of checks and the different between them, some check just one single configuration point, others search for specific security related misconfiguration in multiple resources, this may be challenging to implement, any idea is welcomed!
from prowler.
With that in mind it might be useful to define whatever grading (point, grade, risk) into a file for mapping against the checks that makes it easy for people to edit each level.
from prowler.
So far, the new groups implementation makes easier to create you own report or collection of checks that you need for your organization. Scoring is a nice to have but I want to prioritize now GDPR checks for example, or other compliance related checks that may help us and others improve their security.
from prowler.
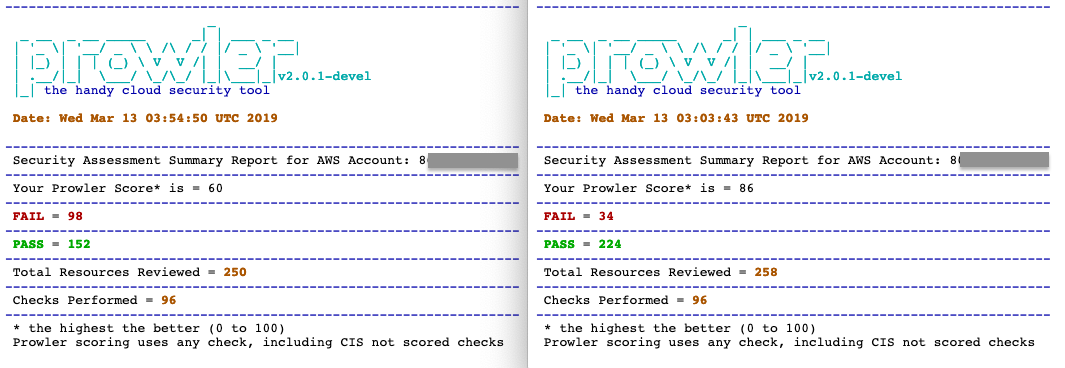
This is now available as a POC in devel branch, option -s
from prowler.
added to master branch, since 2.0.1.
from prowler.
from prowler.
Related Issues (20)
- Allow secrets to be output when explicitly asked for using a flag HOT 3
- [Bug]: prowler azure is not scanning virtual machines in azure HOT 2
- [Bug]: iam_user_console_access_unused.py checks for last password usage HOT 3
- [Bug]: Prowler killed by OOM killer when run in AWS CloudShell HOT 6
- [Feature Request] - Round Robin the base urls in the event of unavailability for indexers HOT 1
- [Bug]: Cross account sqs flagged as public/critical HOT 3
- [Bug]: Exception merging from "*" and specific account HOT 3
- [Bug]: False positive on check - "Check if SQS queues have policy set as Public" HOT 2
- Improve publicly accessible checks to include targets of ELBs HOT 7
- [Bug]: Website Down? HOT 1
- [Bug]: False positve on ec2_securitygroup_not_used with Batch Compute HOT 6
- Support py3.12 HOT 1
- [Bug]: cloudwatch_log_group_retention_policy_specific_days_enabled alert on AWS managed log group HOT 4
- Possibility to custom output file using quick inventory HOT 1
- [Bug]: Output issue HOT 9
- [Bug]: False positive on s3_bucket_policy_public_write_access HOT 1
- [Bug]: allow list reporting wrong findings HOT 3
- [Question]: AWS account security questions have been deprecated HOT 3
- [Question]: Remove S3 KMS check, since its enabed by default, and cant be disabled HOT 2
- [Bug]: The assumed role ARN contains a value for resource type different than role, please input a valid ARN HOT 13
Recommend Projects
-
 React
React
A declarative, efficient, and flexible JavaScript library for building user interfaces.
-
Vue.js
🖖 Vue.js is a progressive, incrementally-adoptable JavaScript framework for building UI on the web.
-
 Typescript
Typescript
TypeScript is a superset of JavaScript that compiles to clean JavaScript output.
-
TensorFlow
An Open Source Machine Learning Framework for Everyone
-
Django
The Web framework for perfectionists with deadlines.
-
Laravel
A PHP framework for web artisans
-
D3
Bring data to life with SVG, Canvas and HTML. 📊📈🎉
-
Recommend Topics
-
javascript
JavaScript (JS) is a lightweight interpreted programming language with first-class functions.
-
web
Some thing interesting about web. New door for the world.
-
server
A server is a program made to process requests and deliver data to clients.
-
Machine learning
Machine learning is a way of modeling and interpreting data that allows a piece of software to respond intelligently.
-
Visualization
Some thing interesting about visualization, use data art
-
Game
Some thing interesting about game, make everyone happy.
Recommend Org
-
Facebook
We are working to build community through open source technology. NB: members must have two-factor auth.
-
Microsoft
Open source projects and samples from Microsoft.
-
Google
Google ❤️ Open Source for everyone.
-
Alibaba
Alibaba Open Source for everyone
-
D3
Data-Driven Documents codes.
-
Tencent
China tencent open source team.

from prowler.