Unifiedbeat reads records from Unified2 binary files generated by network intrusion detection software and indexes the records in Elasticsearch. Unified2 files are created by IDS/IPS software such as Snort and Suricata.
This version is no longer based on a clone of Filebeat, but follows the Beats development guide.
- build from source:
git clone https://github.com/cleesmith/unifiedbeatcd unifiedbeatgo build- if building for linux 64bit platform but on a mac do the following to cross-compile:
env GOOS=linux GOARCH=amd64 go build
- if building for linux 64bit platform but on a mac do the following to cross-compile:
mkdir unifiedbeatcd unifiedbeat- copy or scp the unifiedbeat binary file to the unifiedbeat folder
curl -XPUT 'http://localhost:9200/_template/unifiedbeat' -d@etc/unifiedbeat.template.jsonrm .unifiedbeatif exists ... this file tracks the previous positions within the unified2 files being tailed and indexednano or vim etc/unifiedbeat.ymlthen change YAML configuration file:
- sensor:
- unified2_path: ? # where are the unified2 files, typically: /var/log/snort/snort.log*
- unified2_prefix: "snort.log"
- rules:
- gen_msg_map_path: ? # the absolute full path, typically: /etc/snort/gen-msg.map
- paths: ? # where are the .rules files, typically: /etc/snort/rules/*.rules
- fields: # add fixed/known details about this sensor
- . . .
- output:
- elasticsearch:
- hosts: ["?.?.?.?:9200"] # elasticsearch's ip:port - most securely/typically on the same host as Snort
- elasticsearch:
cp etc/unifiedbeat.yml /etc/unifiedbeat.yml... this is not required but typically done- ./unifiedbeat -c /etc/unifiedbeat.yml
- typically this command would be in a systemd, Upstart, or SysV (init.d) script
- for a quick test use:
nohup ./unifiedbeat -c /etc/unifiedbeat.yml &ps aux | grep -i unifiedbeat... remember it's pid, so you can kill it- use curl, sense, or kibana to look at the indices in elasticsearch
kill ?pid?... when done testing
- now, use Kibana or a custom app daily to see what's up with your host and network ... sleep better at night
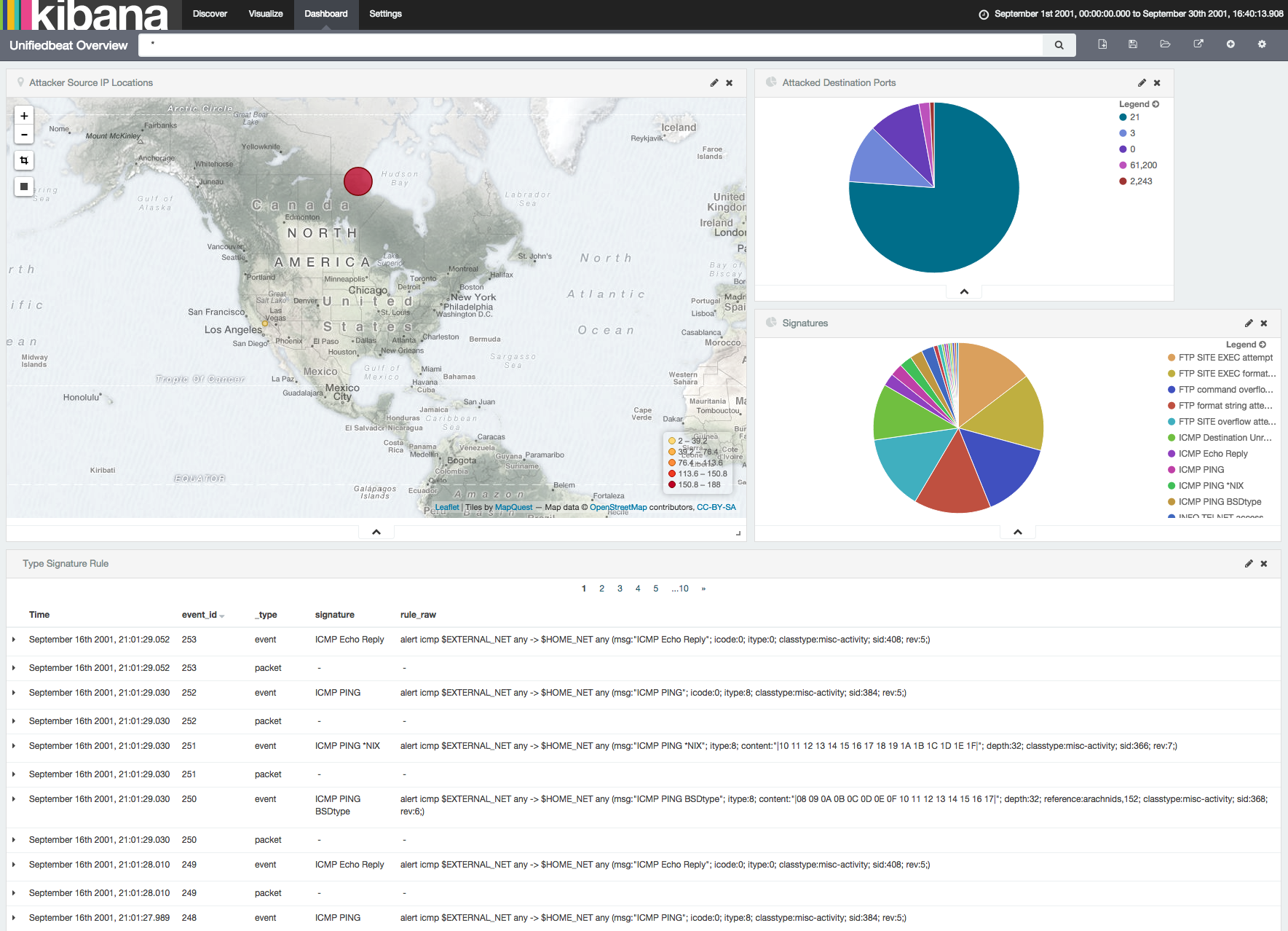
this is just a simple example of a Kibana dashboard and not very useful for security analysts
see kibana/export.json to import the provided dashboard, search, and visualizations into Kibana
new to Kibana? this YouTube playlist is helpful
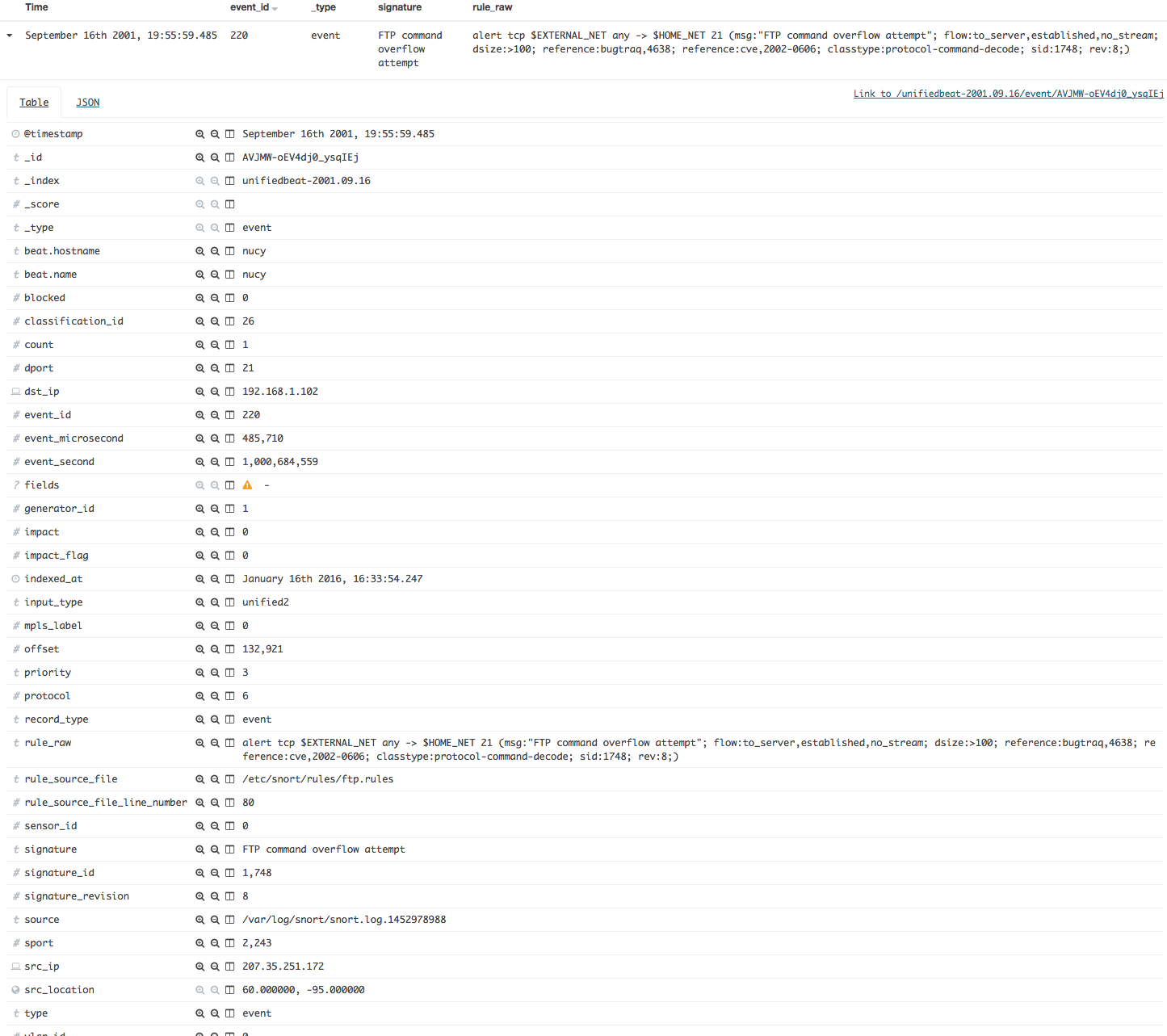
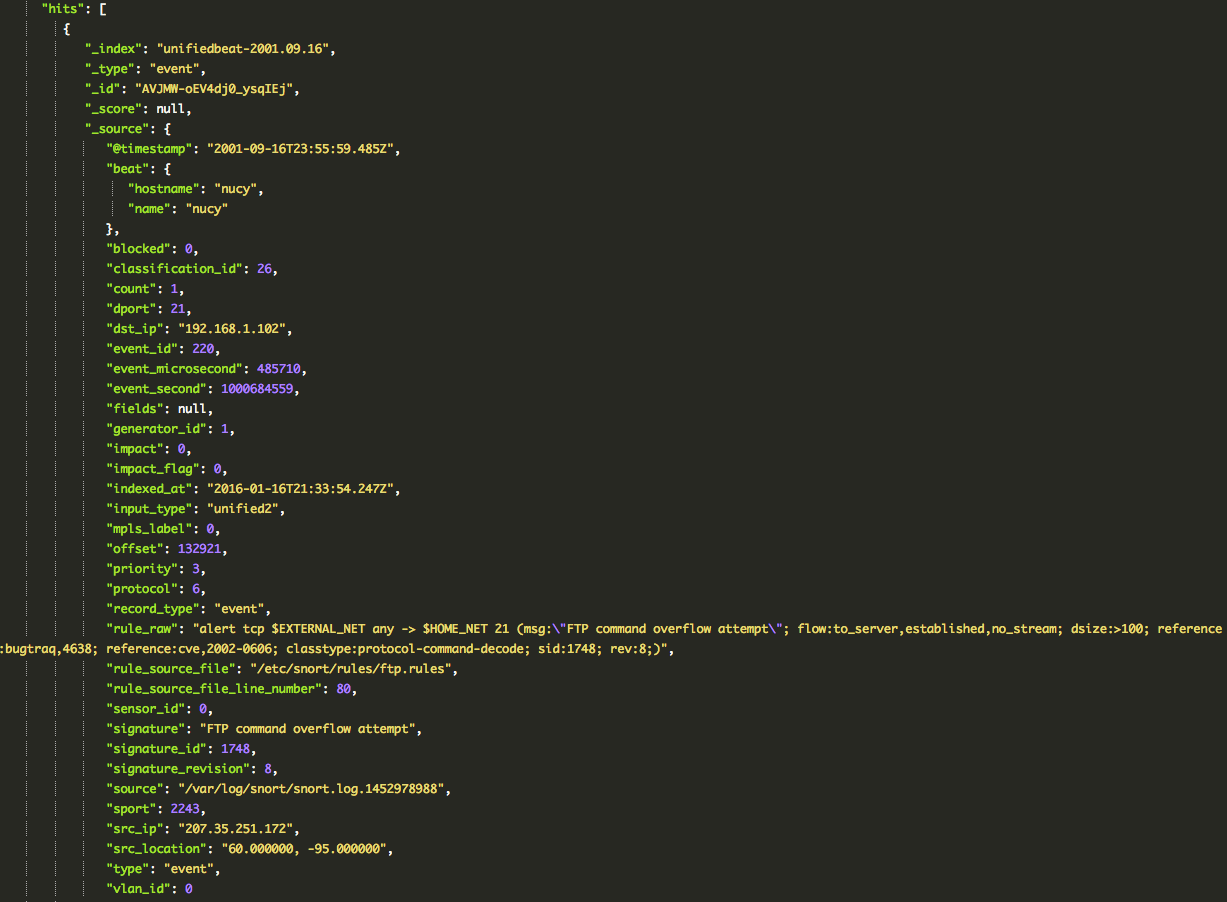
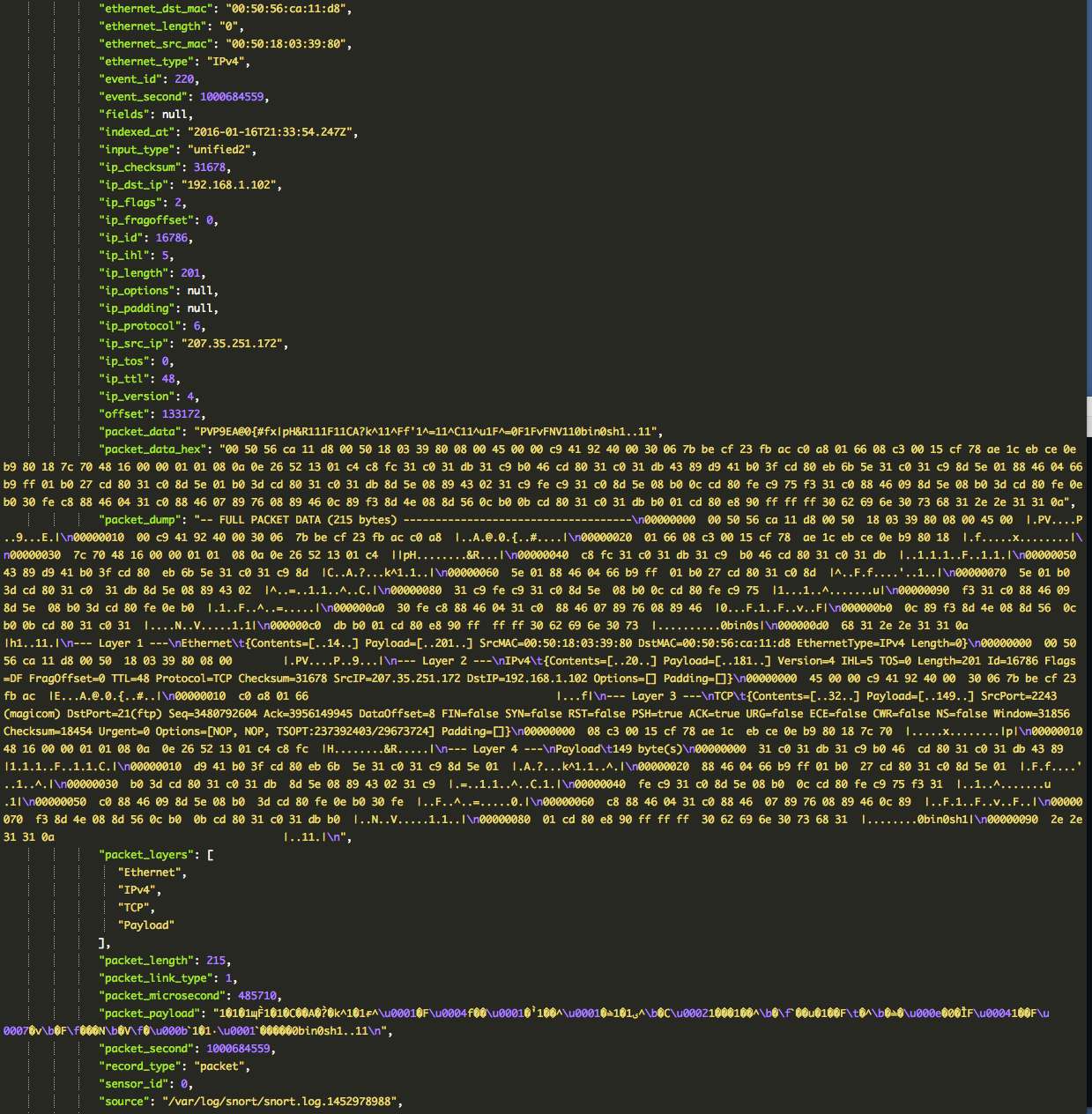
notice the signature and rule_raw fields
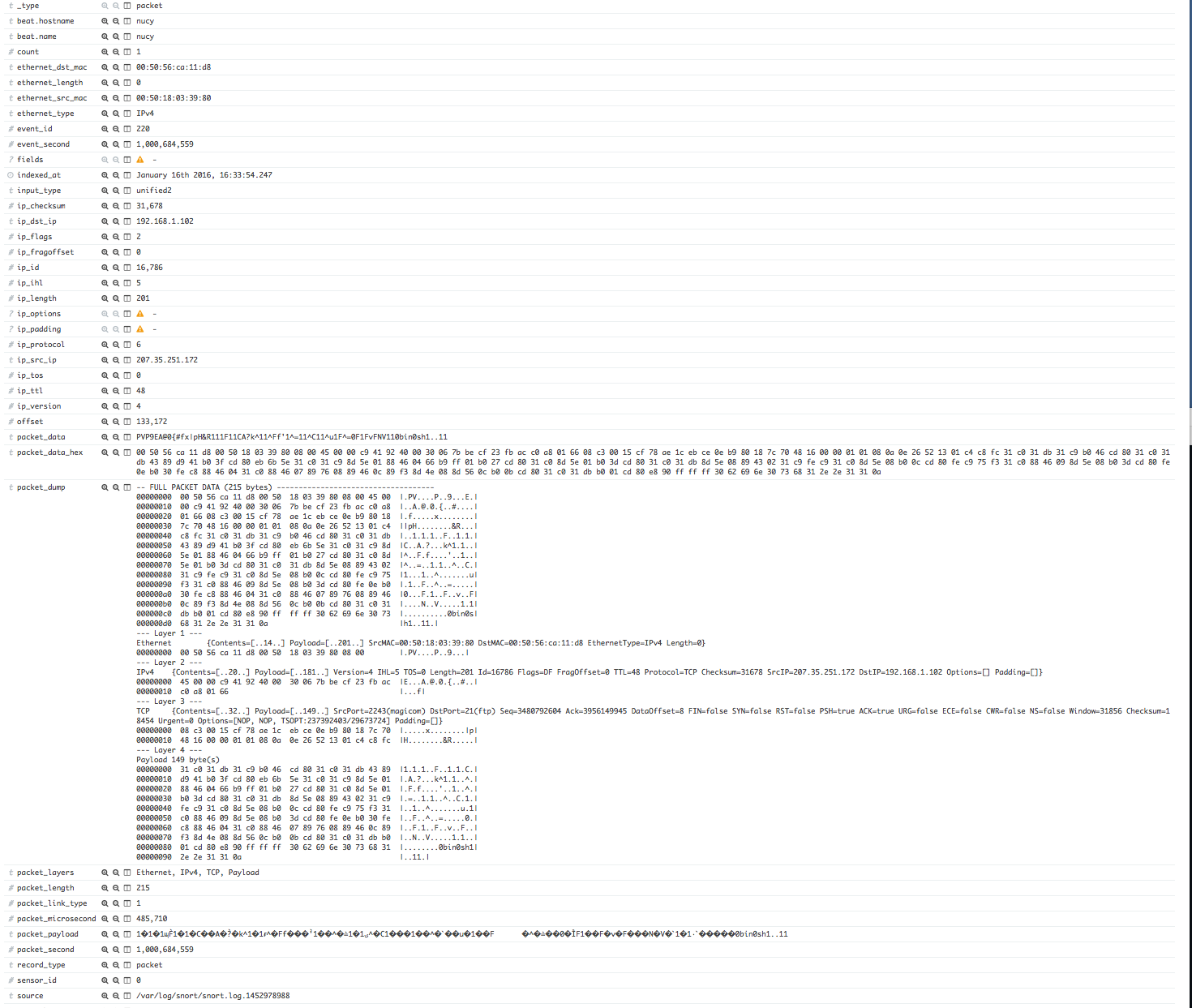
notice the human readable packet_dump field with all layers shown in both hex and text