wangdoc / ssh-tutorial Goto Github PK
View Code? Open in Web Editor NEWSSH 教程
Home Page: http://wangdoc.com/ssh
SSH 教程
Home Page: http://wangdoc.com/ssh
SSH 密钥登录分为以下的步骤。
预备步骤,客户端通过ssh-keygen生成自己的公钥和私钥。
第一步,手动将客户端的公钥放入远程服务器的指定位置。
第二步,客户端向服务器发起 SSH 登录的请求。
第三步,服务器收到用户 SSH 登录的请求,发送一些随机数据给用户,要求用户证明自己的身份。
第四步,客户端收到服务器发来的数据,使用私钥对数据进行签名,然后再发还给服务器。
第五步,服务器收到客户端发来的加密签名后,使用对应的公钥解密,然后跟原始数据比较。如果一致,就允许用户登录。
请问其中对应的公钥是怎么确定的?
OpenSSH 的客户端是二进制程序 ssh。它在 Linux/Unix 系统的位置是/usr/local/bin/ssh,Windows 系统的位置是\Program Files\OpenSSH\bin\ssh.exe。
在上述的描述中,例如windows10的系统位置在C:\Windows\System32\OpenSSH\ssh.exe,而不是\Program Files\OpenSSH\bin\ssh.exe
5.4最后一行
echo "I say:"hello!""
结果应该是I say:"hello!"
文中笔误多了个\
试了 windows 上的 OpenSSH_for_Windows_7.7p1 和 Centos7 上的 OpenSSH_8.0p1, OpenSSL 1.0.2k-fips,都没有 -h 或 -help 参数,请问 client.md 文中的叙述是否有误,什么版本的 OpenSSH 具有该命令?
命令行配置项
-i 默认值为 ~/.ssh/id_rsa
阮老师,“最终效果就是,访问本机的2999端口,就会转发到target-host的2999端口"。这里的2个2999是不是应该是7999呢
服务器一节,PrintMotd配置项的说明中多写了一个the
这是man给出的语法及示例
ssh-keygen -s ca_key -I certificate_identity [-h] [-n principals] [-O option] [-V validity_interval] [-z serial_number] file ...
ssh-keygen supports two types of certificates: user and host. User certificates authenticate users to servers, whereas host certificates authenticate
server hosts to users. To generate a user certificate:**$ ssh-keygen -s /path/to/ca_key -I key_id /path/to/user_key.pub** The resultant certificate will be placed in /path/to/user_key-cert.pub. A host certificate requires the -h option: **$ ssh-keygen -s /path/to/ca_key -I key_id -h /path/to/host_key.pub** The host certificate will be output to /path/to/host_key-cert.pub. It is possible to sign using a CA key stored in a PKCS#11 token by providing the token library using -D and identifying the CA key by providing its public half as an argument to -s: $ ssh-keygen -s ca_key.pub -D libpkcs11.so -I key_id user_key.pub In all cases, key_id is a "key identifier" that is logged by the server when the certificate is used for authentication. Certificates may be limited to be valid for a set of principal (user/host) names. By default, generated certificates are valid for all users or hosts. To generate a certificate for a specified set of principals: $ ssh-keygen -s ca_key -I key_id -n user1,user2 user_key.pub $ ssh-keygen -s ca_key -I key_id -h -n host.domain host_key.pub Additional limitations on the validity and use of user certificates may be specified through certificate options. A certificate option may disable features of the SSH session, may be valid only when presented from particular source addresses or may force the use of a specific command. For a list of valid certificate options, see the documentation for the -O option above. Finally, certificates may be defined with a validity lifetime. The -V option allows specification of certificate start and end times. A certificate that is presented at a time outside this range will not be considered valid. By default, certificates are valid from UNIX Epoch to the distant future. For certificates to be used for user or host authentication, the CA public key must be trusted by sshd(8) or ssh(1). Please refer to those manual pages for details.
在Ubuntu(22.04)中 ChallengeResponseAuthentication 配置项已被替换为 KbdInteractiveAuthentication
建议补充
lpwd
lls
lcd
等操作本地的路径,便于实际使用
请教一下,ssh服务端为什么也需要私钥文件?哪种情况下会用到?
OpenSSH 8.0 支持签名,可考虑添加相关内容:
SSH 客户端一节中
TLS:协议
RSA:密钥交换算法
AES:加密算法
128:加密强度
CBC:加密模式
SHA:数字签名的 Hash 函数
128并不是简单地指加密强度 改成密钥长度会好一些
然后TLS的协议说清楚是什么协议((
现有的这个示例场景比较特殊,是否可以补充一种比较常用的示例以便于理解,以下是大致描述
ssh -R 8080:localhost:80 -N my.public.server
在内网环境下的本机localhost:80开启一个web服务
通过远程转发将这个80端口映射到具有公网IP的my.public.server主机的8080端口上
使得任何人都可以通过my.public.server:8080这个地址访问到本机80端口的web服务
ssh -R [remote-address:]remote-port:target-address:target-port -N remotehost
把本地路由可达的目标端口映射到远程主机的特定端口上,使可通过远程主机的特定端口来访问目标端口
remote address和remote port指定远程的监听地址和端口
target address和target port指定实际被访问的地址和端口,这个地址可以是任何本地路由可达的地址
ref: https://www.ssh.com/academy/ssh/tunneling/example#remote-forwarding
原文 6.1 节,第三步下的说明文字:“这时如果私钥设有密码,ssh 将不再询问密码,而是直接取出内容里面的私钥。”
结合上下文,“内容”似应为“内存”?
本地端口转发 80端口返回403禁止访问 433端口一直处于pending状态 这是什么原因?
谢谢阮老师,想方便离线学习。
文章的这个部分,具体如下图所示:

如上图所示,Host * 如果写在了 Host remoteserver 前面,就无法实现像文中所说的后续覆盖的效果了,因为:

官方文档指出:For each parameter, the first obtained value will be used.(对于每个参数,将使用第一个获得的值)
当 Host * 写在前面时,Port 2222 会被首先使用,下面在补充一个 ssh 连接的过程:
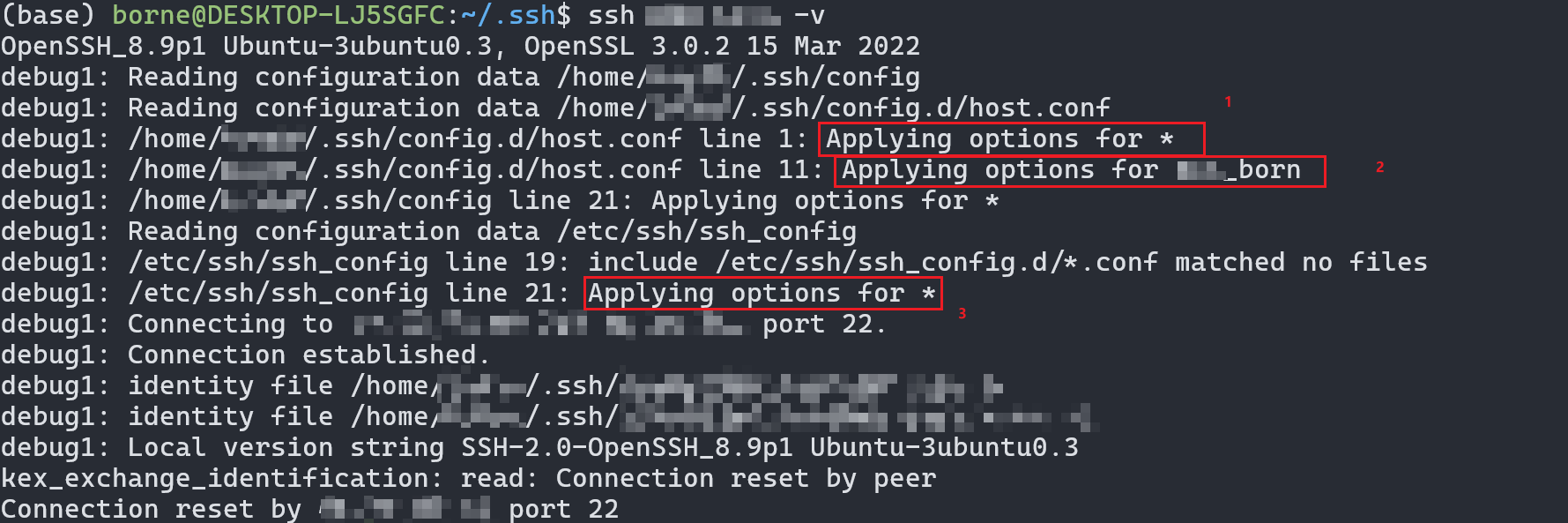
综上所述,要实现文章中所说的写法,应该这样写:
Host remoteserver
HostName remote.example.com
User neo
Port 2112
Host *
Port 2222即:Host * 应该被放到配置文件的最末尾,进行补充设置。
A declarative, efficient, and flexible JavaScript library for building user interfaces.
🖖 Vue.js is a progressive, incrementally-adoptable JavaScript framework for building UI on the web.
TypeScript is a superset of JavaScript that compiles to clean JavaScript output.
An Open Source Machine Learning Framework for Everyone
The Web framework for perfectionists with deadlines.
A PHP framework for web artisans
Bring data to life with SVG, Canvas and HTML. 📊📈🎉
JavaScript (JS) is a lightweight interpreted programming language with first-class functions.
Some thing interesting about web. New door for the world.
A server is a program made to process requests and deliver data to clients.
Machine learning is a way of modeling and interpreting data that allows a piece of software to respond intelligently.
Some thing interesting about visualization, use data art
Some thing interesting about game, make everyone happy.
We are working to build community through open source technology. NB: members must have two-factor auth.
Open source projects and samples from Microsoft.
Google ❤️ Open Source for everyone.
Alibaba Open Source for everyone
Data-Driven Documents codes.
China tencent open source team.